Always the right key
Managing keys is one of the challenges of PGP. From the user's point of view, it would be ideal if the key management could run completely in the background. Mailvelope tries to get as close to this as possible without compromising security. But how should Mailvelope react when it receives an email from an already known recipient, but this message is signed with a new, so far unknown key? Simply accepting the new key would be questionable from a security point of view. This is because, even if the risk is usually low, it could be that someone interested in the contents of the communication is now simply posing as your previous communication partner.
It is therefore clear that these are situations in which it is essential to inform users and advise them about possible risks and ways of reacting. But how exactly can this be done without overwhelming users? With this question, we turned to the UX designers at SimplySecure (aka Superbloom) for help. In the course of our collaboration, interesting results emerged. This is especially true when, as in this case, a real user test environment was used and the "real life reactions" of the users are incorporated in the design process. Kelsey Smith has summarized the considerations that finally led to the solution of the problem in her blog article "Hey, whose keys are these". In the following we will explain how Mailvelope deals with a key change in practice.
Mailvelope detected a new and unknown key
As soon as you receive a message signed with a new key, Mailvelope will display a message informing you about the changed key and giving you some options.
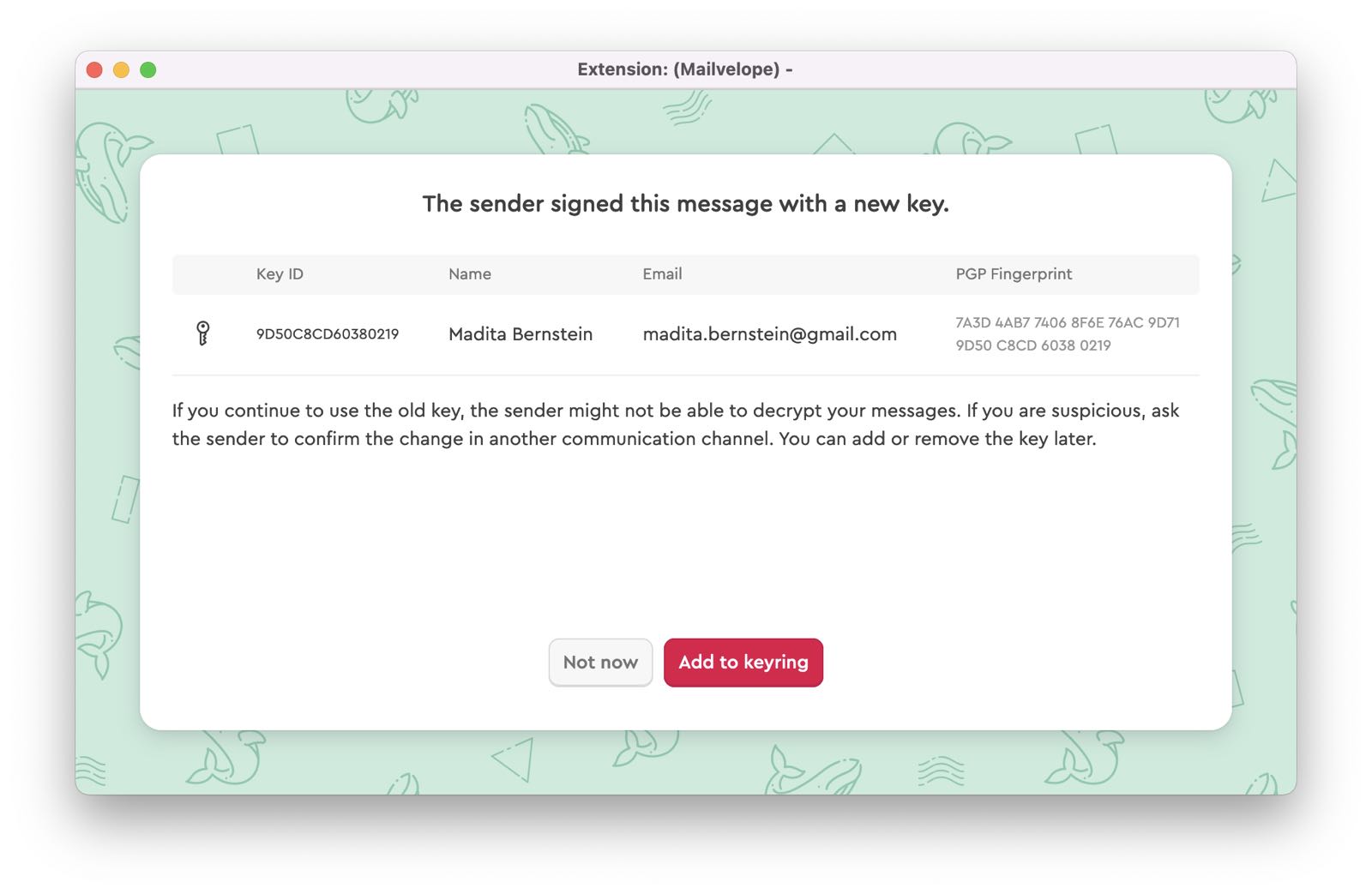
If you want to decide later, click "Not now". This is especially helpful in those situations when you are not sure whether the key is legitimate. We recommend contacting the sender via another communication channel and comparing the PGP fingerprint to confirm. After sucessfull confirmation you might need to reopen the dialog box in order to add the key to your keyring now. Do this by simply clicking on the email which triggered the event and Mailvelope will ask you once more. Keep in mind: If you don’t add the new key, your communication partner might not be able to open your future emails if you are still encrypting with their old key.
Mailvelope can only perform this process with signed encrypted emails. It determines the contact's current key by looking at the most recent valid signature. This information is stored by Mailvelope so that it can automatically select the correct key for future emails to this contact.
This feature is turned on by default, but using it is optional. In order to turn it off, head to "Options" -> "Key Directories" in the Mailvelope settings, and look for the option "Determine current key of contacts and perform key selection automatically". Read more in our FAQ section.
Mailvelope detects more than one key for a recipient while writing an email
In this case you won’t even notice. Every time you want to write an email to a contact which has used several keys in the past, Mailvelope will just choose and display the latest key for writing and encrypting the mail in the Mailvelope editor. This does not mean the other keys are gone: You will easily find them in your Keyring.
Funding and Collaborations
This new feature of Mailvelope was implemented with the help of a grant from Internews. The funding included consulting by the designers from SimplySecure (currently in transformation to "Superbloom"), who are specialized in providing UX design support for software projects. We would like to take this opportunity to thank them for supporting us.